At the beginning of this year, Spectre had sent chills down the spines of everyone in the microprocessor industry. The boffins were somehow able to crack into the Intel CPUs and used it to steal sensitive information, along with other data from the active applications. This major lapse in security enables the user to exploit this vulnerability by using a JavaScript within a web browser, and it can extract passwords and other data from the computer’s memory. It is difficult to counter this problem and requires some major redesigning of the silicon-based chip.

While Spectre may have been detected and quarantined, it seems that Intel can’t catch a break. Researchers at the Worcester Polytechnic Institute in the US and the University of Lübeck in Germany have found yet again a vulnerability that can affect Intel processors. Dubbed as “Spoiler”, it uses the same method as its predecessor, the speculative execution engine (where the processor can predict future commands despite their requirement to enhance performance) to extract information from the cache of the CPUs.
However, what makes this worse that Spoiler is entirely independent of Spectre, which means that the mitigations used for Spectre is virtually ineffective, and no software solution can help to cease this threat. “We have discovered a new microarchitectural leakage which reveals critical information about physical page mappings to user space processes. The leakage can be exploited by a limited set of instructions, which is visible in all Intel generations starting from the 1st generation of Intel Core processors, independent of the OS and also works from within virtual machines and sandboxed environments,” said the researchers in their paper.

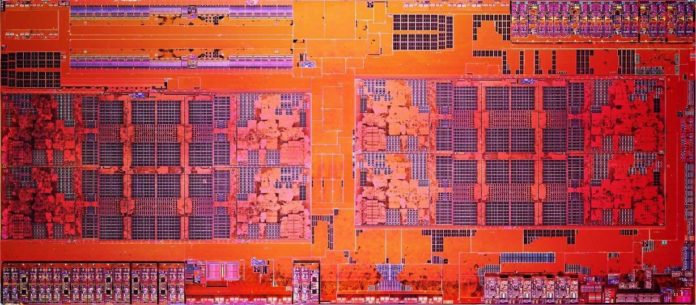
The researchers also claim that AMD and ARM-based processors are somehow immune to Spoiler. It is a relief for AMD because of the nature of the problem; they do not have to roll out software patches to counter these attacks, which tweaks the CPU at the microarchitecture level. AMD has therefore confirmed that Spoiler does not harm the Ryzen processors. “We are aware of the report of new security exploit called SPOILER which can gain access to partial address information during load operations. We believe that our products are not susceptible to this issue because of our unique processor architecture. The SPOILER exploit can gain access to partial address information above address bit 11 during load operations. We believe that our products are not susceptible to this issue because AMD processors do not use partial address matches above address bit 11 when resolving load conflicts,” said the company.
This new threat has created Intel’s problems from bad to worse, whose products are already being regressed from the Spectre patches. Revisiting their architectural designs have become necessary for Intel now so that their processors are immune to Spoiler. Interestingly, the researchers had no particular intention or motive to name this threat as Spoiler. “We picked a named that starts with ‘Sp’ since it’s an issue due to speculative execution and it kinda spoils existing security assumptions on modern CPUs,” said Ahmad Moghimi, member of the research team, to The Register.
Further reading: