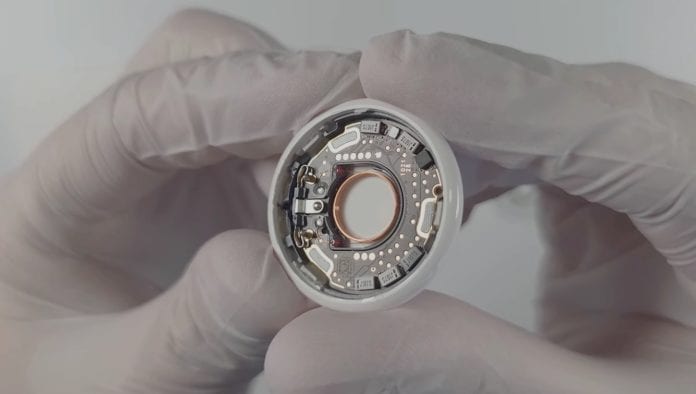
AirTag is not invincible as a security researcher recently discovered that the Cupertino giant’s tracking beacon could be hacked, and it can be reprogramed to change its functions.
Apple is known for its robust security and privacy methodologies, and just like its several other products, AirTag became a challenge for security researchers worldwide. This lead German security researcher YouTuber Stack Smashing to penetrate AirTag security protocols and get a hold over Apple’s recent product just a week after its arrival.
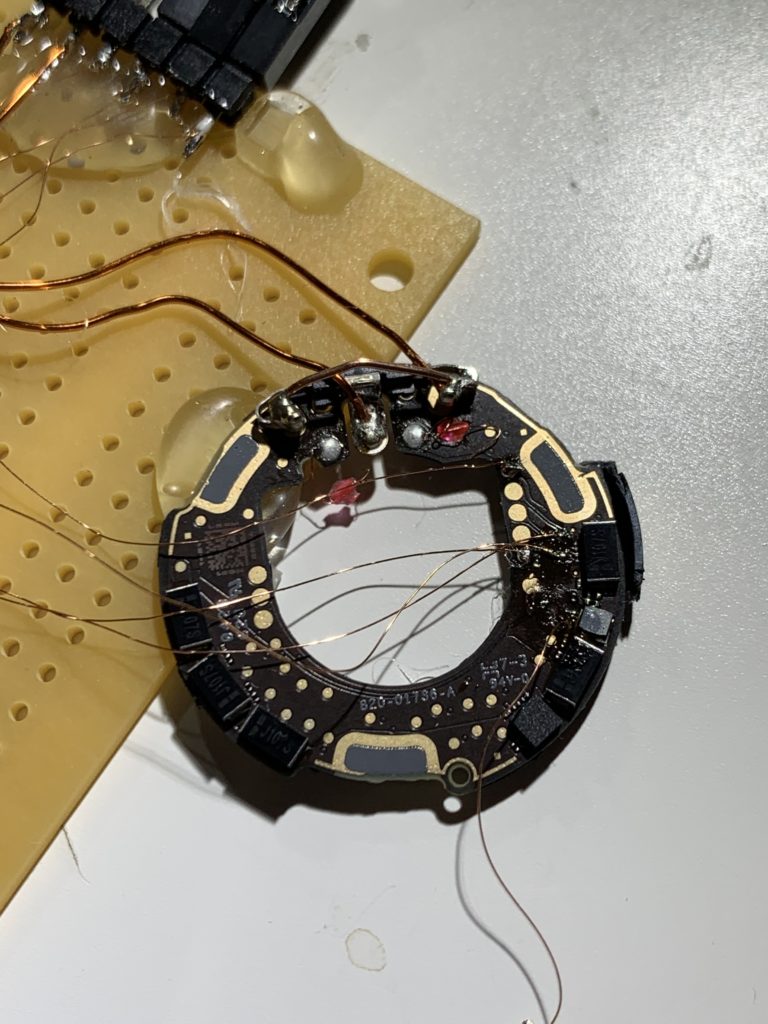
After hours of destruction, the German security researcher was able to break into the microcontroller of the AirTag, which enabled the researcher to re-flash the microcontroller, which in turn allowed them to reprogram AirTag’s software.
What Does This Means?
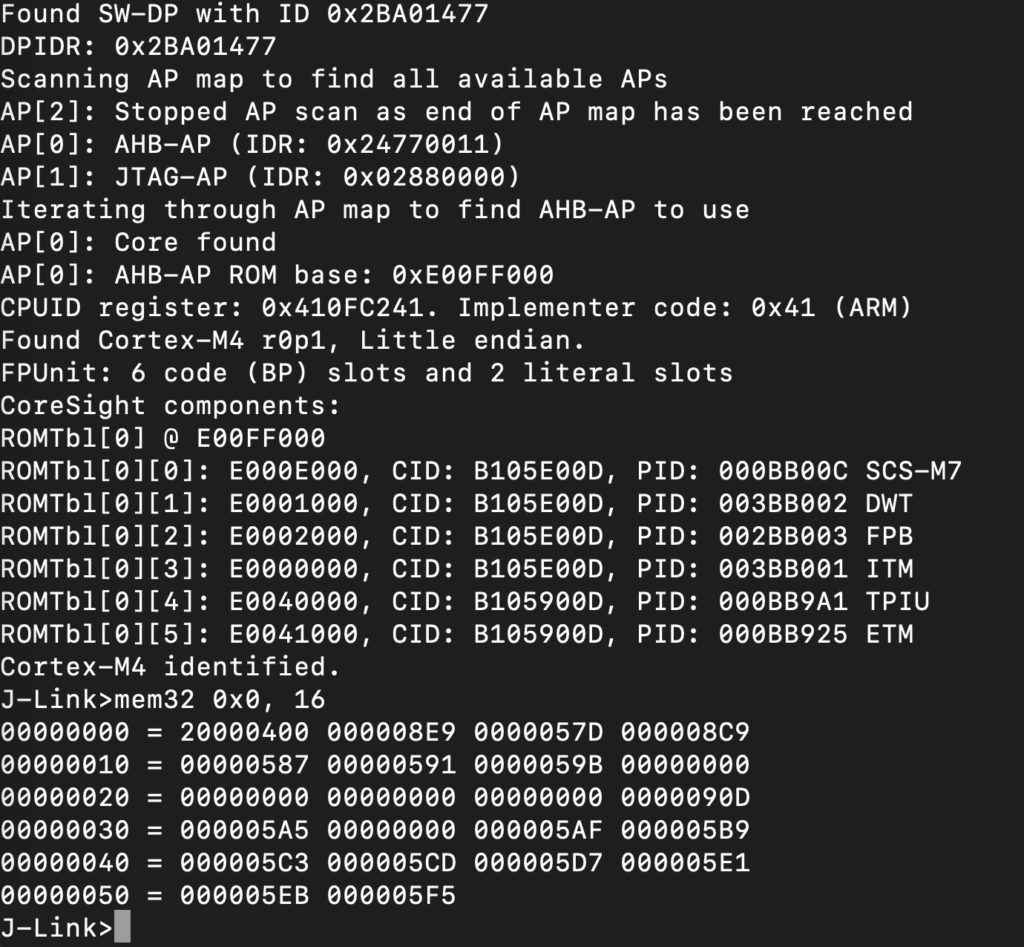
Gaining control over the microcontroller (IC) provides hacker access over the device, in this case, the AirTag, allowing hackers to decide the device’s purpose or functionality. After gaining access over the AirTag, Stack Smashing demonstrated one of the use cases where they changed the NFC URL that appears when an AirTag is in lost mode. The lost AirTag usually redirects to “found.apple.com” to display the owner’s information, but Stack Smashing changed the URL to their website.
This is one of several use cases demonstrated by the Stack Smashing, but attackers could use the loophole for malicious purpose, and Apple would never let this happen. So hacking an AirTag would come with its repercussions to never let this happen. But this is one of the first even where someone has ‘jailbreak an AirTag, and we think a lot can be done other than changing the URL.
We expect Apple to roll out a server-side update as a preventive measure to tackle these malicious AirTag’s. Recently, developers have discovered a hidden debug mode that provides developers with a lot more information than needed.